In 2013, the Westmore News, a small newspaper serving the suburban neighborhood of Rye Brook, New York, ran a element on the opening of a sluice gate at the Bowman Avenue Dam. Costing some $2 million, the new gate, then nearing completion, was developed to reduce flooding downstream.
The party caught the eye of a quantity of community politicians, who gathered to shake fingers at the official unveiling. “I have been to tons of ribbon-cuttings,” county executive Rob Astorino was quoted as indicating. “This is my to start with sluice gate.”
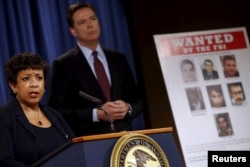
But locals evidently were not the only types with their eyes on the dam’s new sluice. According to an indictment handed down late very last week by the U.S. Section of Justice, Hamid Firoozi, a very well-recognized hacker centered in Iran, attained accessibility quite a few periods in 2013 to the dam’s command programs. Had the sluice been totally operational and linked to those programs, Firoozi could have created serious damage. Luckily for Rye Brook, it was not.
Hack attacks probing critical U.S. infrastructure are absolutely nothing new. What alarmed cybersecurity analysts in this circumstance, on the other hand, was Firoozi’s evident use of an outdated trick that laptop or computer nerds have quietly recognized about for decades.
It is really named “dorking” a search motor — as in “Google dorking” or “Bing dorking” — a tactic long employed by cybersecurity industry experts who function to near stability vulnerabilities.
Now, it appears, the hackers know about it as well.
Hiding in open check out
“What some connect with dorking we truly simply call open-resource community intelligence,” claimed Srinivas Mukkamala, co-founder and CEO of the cyber-chance evaluation agency RiskSense. “It all depends on what you ask Google to do.”
Mukkamala says that research engines are continually trolling the Internet, seeking to file and index every device, port and exclusive IP address linked to the Web. Some of individuals points are developed to be public — a restaurant’s homepage, for case in point — but lots of many others are intended to be non-public — say, the safety camera in the restaurant’s kitchen area. The difficulty, claims Mukkamala, is that as well numerous individuals really don’t recognize the difference just before going on line.
“There’s the World wide web, which is just about anything that is publicly addressable, and then there are intranets, which are meant to be only for interior networking,” he instructed VOA. “The lookup engines will not care which is which they just index. So if your intranet isn’t really configured effectively, which is when you start off observing information and facts leakage.”
Though a restaurant’s shut-circuit digicam might not pose any true security danger, many other issues finding related to the Web do. These include strain and temperature sensors at electrical power plants, SCADA programs that regulate refineries, and operational networks — or OTs — that retain key production plants working.
Irrespective of whether engineers know it or not, many of these matters are becoming indexed by lookup engines, leaving them quietly hiding in open up check out. The trick of dorking, then, is to figure out just how to come across all those property indexed on the web.
As it turns out, it truly is definitely not that tough.
An asymmetric threat
“The detail with dorking is you can generate custom made searches just to glance for that info [you want],” he stated. “You can have a number of nested look for conditions, so you can go granular, enabling you to discover not just every solitary asset, but just about every other asset that is linked to it. You can definitely dig deep if you want,” mentioned RiskSense’s Mukkamala.
Most significant research engines like Google provide innovative look for features: instructions like “filetype” to hunt for particular forms of documents, “numrange” to locate unique digits, and “intitle,” which seems for specific site text. Moreover, distinctive research parameters can be nested one particular in one more, generating a extremely great electronic web to scoop up details.
For instance, as a substitute of just entering “Brook Avenue Dam” into a lookup engine, a dorker may possibly use the “inurl” purpose to hunt for webcams on the web, or “filetype” to glance for command and management documents and capabilities. Like a scavenger hunt, dorking consists of a certain quantity of luck and tolerance. But skillfully utilized, it can considerably improve the opportunity of discovering a little something that should not be general public.
Like most factors on-line, dorking can have good uses as perfectly as negative. Cybersecurity experts more and more use these types of open-source indexing to explore vulnerabilities and patch them prior to hackers stumble on them.
Dorking is also almost nothing new. In 2002, Mukkamala states, he worked on a venture discovering its likely dangers. Extra lately, the FBI issued a community warning in 2014 about dorking, with advice about how network directors could guard their units.
The difficulty, says Mukkamala, is that just about everything that can be related is staying hooked up to the Net, frequently with no regard for its safety, or the protection of the other objects it, in switch, is linked to.
“All you need to have is a single vulnerability to compromise the system,” he advised VOA. “This is an uneven, widespread menace. They [hackers] will not have to have anything at all else than a notebook and connectivity, and they can use the tools that are there to start launching assaults.
“I never assume we have the knowledge or assets to defend in opposition to this menace, and we are not geared up.”
That, Mukkamala warns, means it truly is far more probably than not that we are going to see more scenarios like the hacker’s exploit of the Bowman Avenue Dam in the several years to occur. Sad to say, we may possibly not be as lucky the up coming time.